A massive data breach has sent shockwaves through the digital landscape, with leaked records unveiling sensitive information about organizations. The fallout is already catastrophic, eroding the reputation of institutions involved and igniting widespread anxiety among members.
The leaked data, which reportedly includes names, has been circulating widely online, {putting{ individuals at risk of harassment. Experts warn that the lasting impact of this breach could be extensive, highlighting the urgent need for stronger privacy measures.
- Regulators are currently investigating into the breach, aiming to uncover the origin and the extent of the damage.
- Businesses affected by the leak are {working to mitigate{ the impact and extend help to users.
- The public are encouraged to be aware of potential scams and to {take steps{ to protect their own data.
Digital Footprint Fallout|
In the digital age, our every action leaves an indelible trace on the vast expanse of the internet. What we share online, from casual updates to carefully curated profiles, becomes a lasting record that can follow us throughout our lives. This trail of digital breadcrumbs, known as our digital footprint, can have profound consequences on our future prospects, relationships, and even personal identity.
A single message, seemingly innocuous at the time, can explode into a controversy years later, creating a shadow over our career. Employers may scrutinize our online behavior, and potential acquaintances might stumble upon past behaviors that paint an problematic picture. The internet, once a realm of freedom and expression, can become a double-edged sword, exposing our vulnerabilities and shadowing us with the burden of our digital past.
Reputation on Thin Ice: Leaks Expose Hidden Truths in Breaking News Cycle
In today's volatile/hyperactive/chaotic news cycle, where information spreads like wildfire and public opinion/perceptions/mindsets shift rapidly/constantly/momentarily, read more reputation has become an ever-fragile/precarious/tenuous entity. Recent leaks/disclosures/exposés have ripped through the veil of deception/spin/concealment, exposing hidden truths and revealing the stark/unflinching/harsh realities behind carefully crafted narratives. What was once considered irrefutable/undisputed/definitive is now subject to intense scrutiny/public dissection/critical analysis, leaving individuals and institutions grappling with the consequences/ramifications/aftershocks of their actions.
The speed at which news travels, coupled with the pervasive influence of social media, means that any lapse/slip-up/breach in trust can quickly spiral into a full-blown crisis/scandal/meltdown. Organizations/Individuals/Public figures once held in high esteem find themselves fighting for their credibility, as leaked information erodes their carefully cultivated image and casts doubt on their motives.
This phenomenon raises important questions about the nature/ethics/impact of leaks in a digital age. Are they acts of courage/whistle-blowing/transparency or simply harmful disclosures/betrayals/sabotage? What are the boundaries/limitations/responsibilities of those who possess sensitive information? And how can we navigate this complex landscape to ensure that truth prevails while protecting individual rights and preserving public trust/maintaining social order/fostering accountability?
Managing the Digital Firestorm After a Leak
A data leak can ignite a digital firestorm, rippling through social media and news outlets with alarming speed. In these critical moments, swift and calculated action is crucial. A well-structured crisis control plan can help contain the damage, protect your reputation, and reclaim trust with stakeholders.
First and foremost, recognize the leak publicly and convey genuine concern for those affected. Transparency is critical to establishing confidence. Outline the magnitude of the breach, the steps you're taking to determine the cause, and the strategies in place to prevent future incidents.
Interact proactively with your customers, providing regular information on your progress. Harness multiple channels, including social media, press releases, and dedicated communications to reach a wider base. Remember, in a crisis, silence can be the most significant enemy.
The Algorithmic Echo Chamber: The Impact of Leaks on Public Opinion
In the digital age, information spreads at an unprecedented rate. While, this flood of data can be a double-edged sword. While it empowers individuals with access to a wealth of knowledge, it also creates fertile ground for the formation of algorithmic echo chambers. These virtual spaces, fueled by sophisticated algorithms, tend to echo existing beliefs and suppress dissenting voices. Leaks, often disclosed in a chaotic manner, can become potent catalysts in this phenomenon.
As a result, public perception can be fundamentally shaped by these leaks, sometimes distorting the nuance of an issue. Public scrutiny becomes paramount in navigating this complex landscape.
- Furthermore
- Considerably
Unmasking the Anonymous: Leaks and the Erosion of Trust in the Digital Age
In an era electronic characterized by unprecedented communication, the anonymity afforded by the internet has fostered a double-edged sword. While enabling expression of thought and coordination, it also provides a platform for malicious actors to propagate harmful content and undermine structures. Disclosures have become increasingly common, exposing sensitive information and eroding public confidence in governments. This erosion of trust has far-reaching consequences, threatening the fabric of our social systems. Combating this issue requires a multifaceted approach, encompassing stricter policies, improved cybersecurity protocols, and a renewed emphasis on transparency. Ultimately, restoring trust in the digital age demands a collective effort to foster a more secure and ethical online environment.
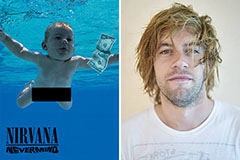 Spencer Elden Then & Now!
Spencer Elden Then & Now! Bug Hall Then & Now!
Bug Hall Then & Now! Tonya Harding Then & Now!
Tonya Harding Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now! Ryan Phillippe Then & Now!
Ryan Phillippe Then & Now!